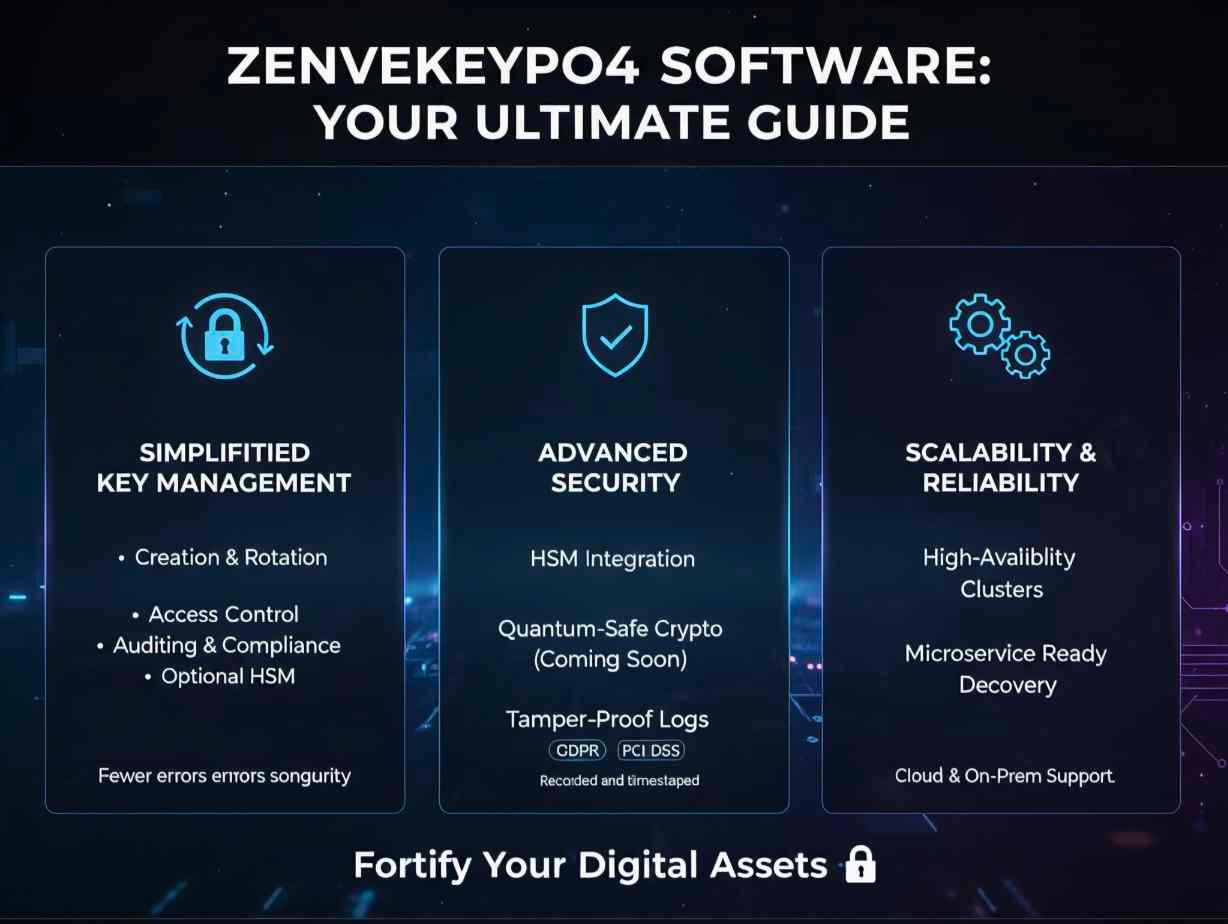
Unlocking the Power of zenvekeypo4 software: Your Ultimate Guide
In today’s fast-paced digital world, security and key management have never been more important. Enter zenvekeypo4 software, a next-generation solution designed to streamline encryption key handling, API secrets, and application credentials across your enterprise. Whether you’re a developer, an IT administrator, or a security professional, understanding this platform—and how it supports your organization’s goals—is critical. In this article, we’ll dive deep into its features, benefits, installation tips, and real-world applications, all in plain language.
Understanding What zenvekeypo4 software Really Is
At its core, zenvekeypo4 software is a comprehensive encryption key management system that integrates seamlessly with modern DevOps workflows. Unlike scattered tools or built-in OS utilities, this platform centralizes key storage, automates key rotation, and provides audit logs for compliance. It supports cloud, on-premises, and hybrid environments—so whether your infrastructure is legacy or cutting-edge, you’re covered.
The role of centralized key management
When organizations rely on multiple applications, microservices, and APIs, keeping track of keys becomes a nightmare. With a unified solution like zenvekeypo4 software, you gain a single pane of glass, making it easier to enforce policies, reduce vulnerabilities, and simplify encryption management across the board.
Integration with modern toolchains
It’s not enough to manage keys in isolation. The best practices involve embedding key management within CI/CD pipelines, container orchestration platforms, and automated testing—even chatops. The platform supports RESTful APIs, SDKs, and command-line interfaces, making it highly adaptable in ever-changing environments.
Key Features That Set It Apart
One of the biggest differentiators of zenvekeypo4 software is its rich feature set built for today’s security demands.
Simplified key lifecycle management
From generation to destruction, the tool helps with every phase: key creation, versioning, usage tracking, rotation, and archival. That means fewer manual errors, fewer forgotten keys, and stronger overall security.
Real-time audit trails and compliance
Auditing isn’t just a checkbox anymore. With this software, every key access attempt, usage, or change is recorded and timestamped. That helps with regulatory requirements (such as GDPR, PCI-DSS) and internal governance.
Secure API and microservice support
Modern software architectures use microservices and APIs heavily. The zenvekeypo4 software offers built-in support for securing those API secrets and ensures your services talk securely. Malicious actors targeting weak credentials become a thing of the past.
How to Get Started with zenvekeypo4 software
Getting up and running with a complex tool can feel daunting—but this software is designed with usability in mind.
System requirements and setup
First, check your environment: you’ll need a supported operating system (Windows, Linux, or containerized environment), sufficient RAM and storage, network access for the key management cluster, and optionally a hardware security module (HSM) if you require top-tier protection. Installation is typically handled via installer or container image, and a wizard walks you through basic configuration.
Best practices for initial configuration
Once installed, you’ll want to define roles and permissions clearly—who can generate keys, who can use keys, and who can view audits. Next, establish your key rotation policy: for example, rotate keys every 90 days or after device changes. Then integrate with your CI/CD pipeline and container orchestration tool so that every service receives its secrets programmatically rather than manually.
Real-World Use Cases and Benefits
Understanding why you’d adopt zenvekeypo4 software is just as important as understanding how. These are the most compelling scenarios.
Protecting sensitive application data
In industries like finance, healthcare, or e-commerce, protecting customer data is non-negotiable. The software enables encryption of data at rest and in motion, with keys managed centrally and transparently. That means fewer data breaches and stronger customer trust.
Supporting DevOps and agile teams
DevOps teams are under pressure to deploy features fast while maintaining security. With automated key rotation and API secret management via zenvekeypo4 software, teams avoid delays and reduce bottlenecks. Secrets are injected securely into containers or servers, leaving no “key .txt on a dev server” scenario.
Simplifying regulatory compliance
Regulations like SOX, HIPAA, and ISO 27001 require strict controls over who accesses encryption keys and when. The platform’s audit trails, role-based access controls, and encryption support make compliance simpler and less painful during audits.
Challenges to Consider and How to Overcome Them
Even the best tools require thoughtful planning. Before adopting zenvekeypo4 software, be aware of potential pitfalls and how to manage them.
Organizational buy-in and training
Security tools are only as strong as the people using them. Teams must be trained in key management concepts, role assignments, and operational procedures. Failure to train can lead to misconfigurations—so allocate time for workshops or training sessions.
Migration of legacy systems
If your organization has old systems storing keys in files or environment variables, migrating to a centralized platform can be tricky. Plan a phased migration, audit all existing key stores, map dependencies, and gradually retire what is no longer required. Using a tool like zenvekeypo4 software can ease this process significantly.
Ongoing governance and maintenance
Key management is not a one-off task—it’s ongoing. The biggest risk is setting it up and forgetting about it. With zenvekeypo4 software, you’ll want to assign ownership for monitoring, auditing, rotating, and retiring keys. Build this into your operational calendar to avoid lapses.
FAQ’s
Q1: What platforms does zenvekeypo4 software support?
A: It supports Windows, Linux, containerized environments, and integrates with public clouds, on-premises, or hybrid infrastructures.
Q2: How often should I rotate keys using this tool?
A: Great question—industry practice suggests every 60–90 days or when a system change happens. The platform makes automation of rotation much easier.
Q3: Can I integrate zenvekeypo4 software with existing CI/CD tools?
A: Yes. The software provides REST APIs, SDKs, and plugins that integrate with common CI/CD tools and orchestration platforms.
Q4: What happens if I lose access to the key management system?
A: The solution supports high-availability configurations and disaster recovery protocols. Make sure you configure backup and failover correctly from the start.
Q5: Will using this tool help with regulatory compliance?
A: Absolutely. By providing centralized key management, audit trails, role-based access, and policy enforcement, it supports your compliance posture across standards like GDPR, PCI-DSS, and ISO 27001.
Conclusion
In a time when digital transformation is accelerating and cyber-threats are evolving by the minute, adopting a robust solution like zenvekeypo4 software can make a tangible difference. From centralized encryption key management to streamlined DevOps integrations and regulatory support, it addresses the full lifecycle of keys and secrets in your ecosystem. Of course, successful adoption means aligning people, processes, and technology: secure policies, training, and governance are essential. But with the right approach, security becomes an enabler rather than a blocker. If you’re looking to bring clarity, control, and confidence back into your encryption strategy, this tool is well worth serious evaluation.